Social engineering, in broad terms, is the act of influencing someone to take a specific action. It’s often said that social engineers use our human nature against us. They manipulate our trust in order to get us to do what they want, whether that’s surrendering our personal information or taking actions that put University information at risk.
Traditionally, social engineers ran their cons in person. With the advent of the digital age, however, hackers immediately took to social engineering as a means of getting data or system access by using their perceived anonymity to con people into trusting them. The consensus among security experts is that social engineering is the basis for most data breaches, and it represents significant risk to unaware users.
How does social engineering work?
In order to influence others, hackers need to build trust. Trust is what makes a potential victim less likely to question the hacker and more likely to provide information to him or her.
In order to successfully build trust with you, hackers rely on pretexting. Pretexting is the act of establishing a context for a specific situation, specifically to facilitate a con. In social engineering, hackers disguise their true intentions by using pretexting to establish a seemingly legitimate need for your information.
Examples of pretexting include posing as an account manager at a bank to request your financial information, or posing as a customer service representative at a retail store to request a credit card number.
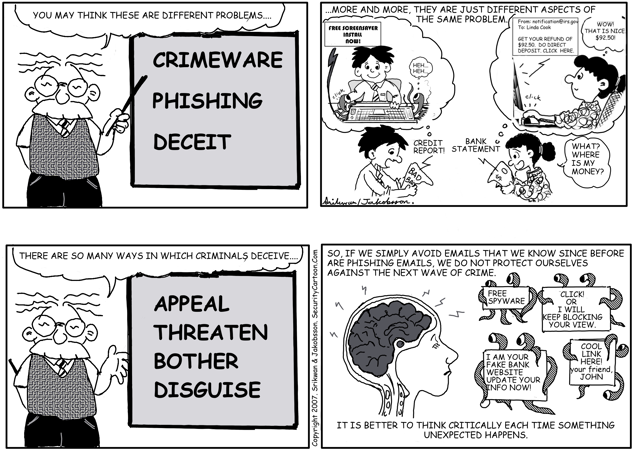
Social engineering scams use several general tactics while pretexting:
- Impersonation – The hacker may impersonate a legitimate individual or organization to lull you into a false sense of security.
- Urgency – The hacker may create a false sense of urgency to trick you into taking action before thinking.
- Innocence – The hacker may ask seemingly harmless questions to trick you into surrendering personal information without your realizing how important it is.
What are social engineering tools?
Because the hacker wants access to your device or your information, he or she needs to interact with you in some way. Interaction allows the hacker to deceive you. Hackers using social engineering have a variety of ways to contact you:
- Email messages –Hackers can use phishing scams to trick you into visiting a malicious website, downloading malware, or replying with information.
- Phone calls –They can use vishing scams (a portmanteau of voice and phishing) to trick you into surrendering information or clicking or texting when you shouldn’t.
- Web sites – They can use malicious Web sites to deliver malware, harvest information, or trick you into entering information.
Hackers and con artists use all these tactics to trick you into surrendering important or confidential information.
 Reproduced with permission. Please visit www.SecurityCartoon.com for more material.
Reproduced with permission. Please visit www.SecurityCartoon.com for more material.
What is the threat?
Social engineering presents two major threats.
First, it’s easy for scam artists to get information by deceiving their victims. Hackers can spend months cracking data or trying to overpower or sneak through security systems, but they can spend mere minutes writing phishing emails or dialing vishing scams to get the same result. Social engineering requires less effort and yields greater success because it pits the hacker not against a hardened security system but against a potentially naive and trusting human being.
Second, it’s hard to detect successful social engineering schemes. Because these schemes build trust with their victims, they usually go unquestioned, so it’s not always apparent that devices and information have been compromised. If the scam is not caught as it is being launched, it probably won’t be detected until serious damage is done to or with the compromised system. Some scams may never be detected.
Because of its potential to do great harm without raising alarm, social engineering is highly dangerous to both individuals and organizations. Successful schemes can compromise extremely valuable systems and data, yet remain completely undetected because of the victims’ trust. Always be cautious, and verify information before taking action. Don’t give personal or organizational information to anybody you aren’t certain has a right to it.
